 Hello All. Yes, you heard me, Sysmon is coming natively to Windows in 2026.
Hello All. Yes, you heard me, Sysmon is coming natively to Windows in 2026.
Mark Russinovich, the creator of Sysmon, recently posted this amazing news on the Windows IT Pro Blog:
“Next year, you will be able to gain instant threat visibility and streamline security operations with System Monitor (Sysmon) functionality natively available in Windows!
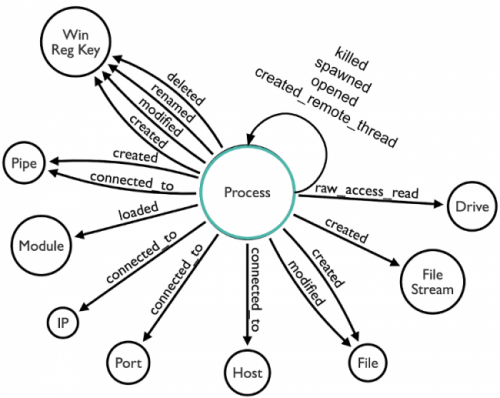
Part of SysInternals, Sysmon has long been the go-to tool for IT admins, security professionals, and threat hunters seeking deep visibility into Windows systems. It helps in detecting credential theft, uncovering stealthy lateral movement, and powering forensic investigations. Its granular diagnostic data feeds security information and event management (SIEM) pipelines and enables defenders to spot advanced attacks.
But deploying and maintaining Sysmon across a digital estate has been a manual, time-consuming task. You’ve downloaded binaries and applied updates consistently across thousands of endpoints. Operational overheads introduce risk when updates lag. And a lack of official customer support for Sysmon in production environments poses added risk and additional maintenance overhead for your organization.”
With this update, you will be able to easily activate Sysmon in Windows 11 and Windows Server 2025 with the simple command: sysmon -i at the cmd.exe prompt. This should be coming in 2026 as part of a Windows Update.
According to Microsoft’s roadmap, Sysmon will be available through the built‑in Optional features mechanism in Windows. Administrators will be able to install Sysmon using standard OS tools, without downloading a separate package, and updates will be delivered directly via Windows Update.
Here is the original post: https://techcommunity.microsoft.com/blog/Windows-ITPro-blog/native-sysmon-functionality-coming-to-windows/4468112
