Hello All. VMware has shipped updates to address two security vulnerabilities in vCenter Server and Cloud Foundation that could be abused by a remote attacker to gain access to sensitive information.
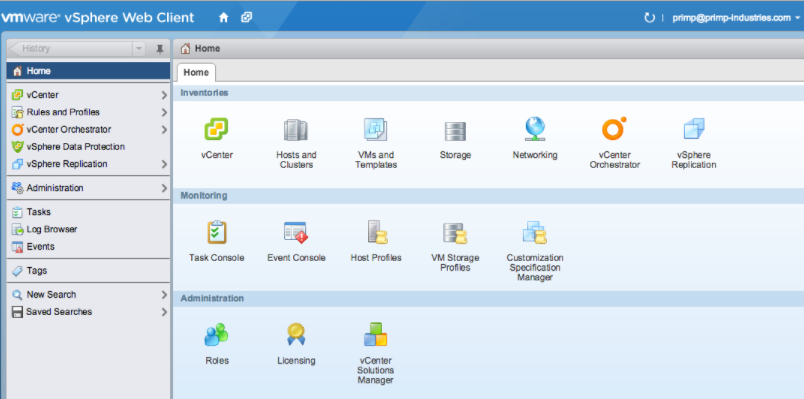
The more severe of the issues concerns an arbitrary file read vulnerability in the vSphere Web Client. Tracked as CVE-2021-21980, the bug has been rated 7.5 out of a maximum of 10 on the CVSS scoring system, and impacts vCenter Server versions 6.5 and 6.7.
“A malicious actor with network access to port 443 on vCenter Server may exploit this issue to gain access to sensitive information,” the company noted in an advisory published on November 23, crediting ch0wn of Orz lab for reporting the flaw.
The second shortcoming remediated by VMware relates to an SSRF (Server-Side Request Forgery) vulnerability in the Virtual storage area network (vSAN) Web Client plug-in that could allow a malicious actor with network access to port 443 on vCenter Server to exploit the flaw by accessing an internal service or a URL request outside of the server.
The company credited magiczero from SGLAB of Legendsec at Qi’anxin Group with discovering and reporting the flaw.
Further information can be found at: